Expired certificates aren't bad luck – they're a process failure
4. Feb 2026Monday morning, 08:30.
A critical application fails to start. Monitoring systems show alerts everywhere - yet at first glance the infrastructure looks fine. After about 40 minutes of intensive log analysis, the root cause is finally identified: a TLS certificate has expired.
The real problem in these situations isn’t that certificates expire - it’s that nobody on the team knows exactly who owns the certificate, where the private key is stored, or why it doesn’t appear in any inventory.
Does this sound familiar? Our experience shows this isn’t a technical issue - it’s a process issue.
In a world with hybrid clouds, microservices, and thousands of machine identities, Certificate Lifecycle Management (CLM) is no longer a niche topic. It has become a critical operational function - not a technical detail to be remembered once a year.
DownloadTL;DR – What you'll find in this article
If you’re short on time right now, feel free to save this article for later. It covers:
- a five-building-block framework for effective Certificate Lifecycle Management (CLM)
- common warning signs that indicate a high risk of outages
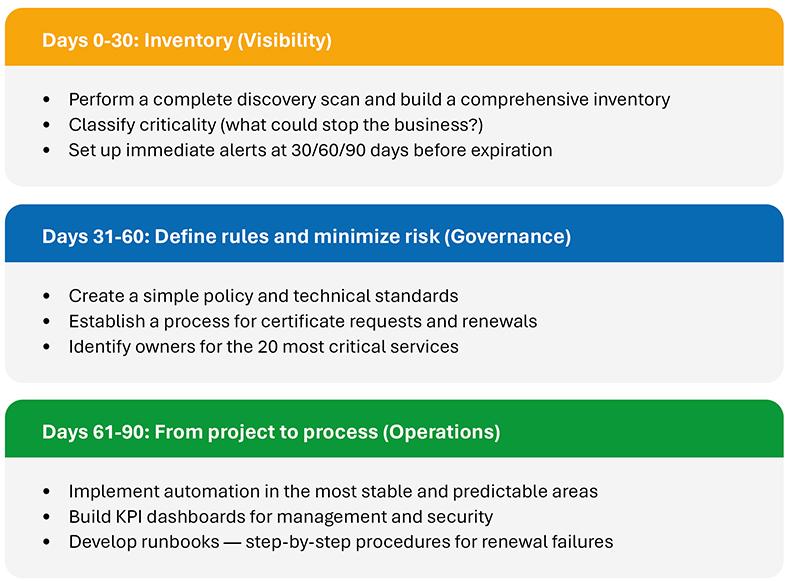
- a 90-day playbook, from inventory to a stable, repeatable process
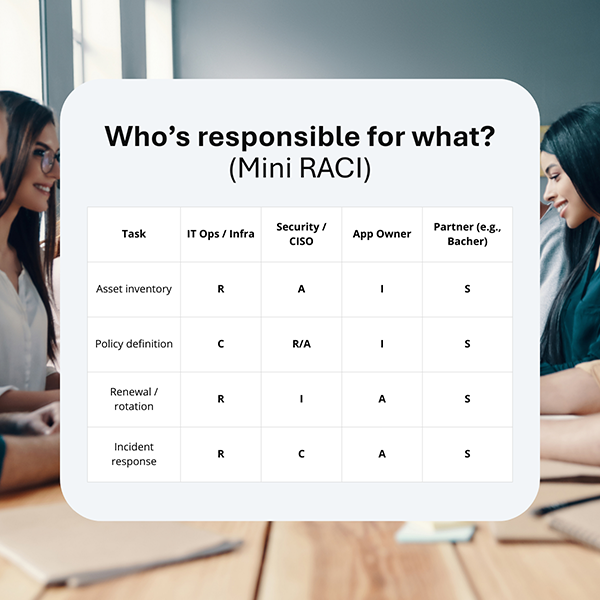
- a responsibility matrix (RACI) that clarifies roles and ownership
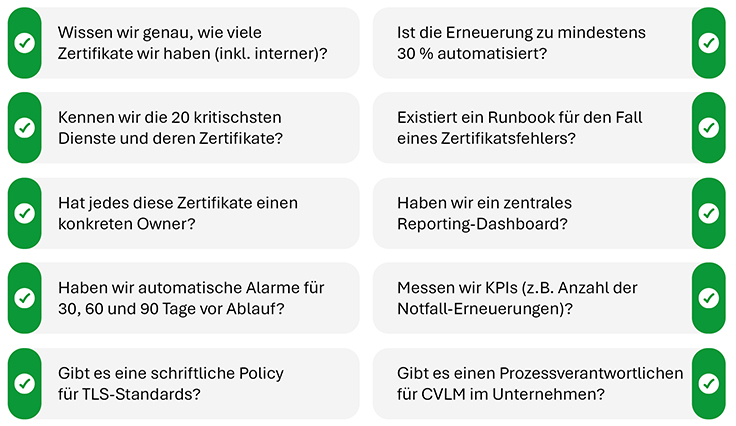
- a checklist to help you realistically assess your environment
Why you should address this now
Not long ago, certificate management was manageable: a handful of domains, one provider, renewals every two years. Today IT reality is very different:
- Certificate volume explosion: Containers, APIs, IoT, multi-cloud - each environment requires its own identities.
- Shorter validity periods: Security standards force more frequent rotations, and manual processes no longer scale.
- Increasing compliance pressure: In regulated environments, audits don’t just check whether you use certificates - they evaluate how you manage renewals
The question is not whether a certificate will expire - it will. The key question is: Do you find out in time? And does your organization have a process that enables renewal without chaos?
Typical indicators of organizational chaos
Before we discuss solutions, check whether any of these scenarios are familiar:
- Incomplete inventory: “We don’t know exactly how many certificates we have or where they are used.”
- Excel as the “central system”: Renewals are tracked in spreadsheets or emails that often reference former employees.
- Unclear ownership: The infrastructure team points to security, and security points to application teams.
- Last-minute incidents: The process only begins once users already see “Connection not secure” warnings and cannot access the application.
Remember: Automation without clearly defined responsibilities is a reliable recipe for chaos.
5 elements of effective CLM
To prevent certificate management from becoming a constant firefight, a stable framework is necessary. At Bacher Systems, we work with five core components:
- Inventory & Discovery: You can only protect what you know exists. Continuous discovery of all certificates - both public and internal - is the first step.
- Ownership: Every certificate needs a clearly defined owner. Shared responsibility almost always leads to outages.
- Policy & Governance: Clear rules create reliability. Which CAs are permitted? What key lengths are acceptable? The goal is a minimum viable policy - concise, understandable, and enforceable.
- Renewal & Rotation: Automate request, distribution, and installation where processes are stable and well-defined.
- Monitoring & Reporting: Dashboards show certificate status and risk, moving from reactive firefighting to proactive operations.
Implementation plan: a 90-day playbook
Who is responsoble for what? (Mini RACI)
The biggest challenge in CLM isn’t the tools - it’s the people. Establishing a clear RACI (Responsible, Accountable, Consulted, Informed) model helps eliminate ambiguity and ensures the right teams are accountable for CLM outcomes:
Case study: From outages to operational resilience
In an organization we worked with, certificate renewal typically took five workdays and involved four people. Emails, tickets, and manual key copying made the process error-prone - and one forgotten certificate nearly brought down the entire payment system.
After implementing a complete CLM cycle, effort dropped to minutes and visibility reached 100%.
Our approach at Bacher Systems: the Adoption Cycle
Certificate management is not a one-off tool deployment - it is continuous operational work. Our Adoption Cycle model includes:
- Consulting: Analyze current state and gaps.
- Implementation: Select appropriate tools and design processes.
- Operations: Support day-to-day operations, updates, and patching.
- Optimization: Ongoing reduction of exceptions and increased automation.
We take responsibility for the outcome - not just the technology.
Checklist: Is your CLM under control?
Ask yourself and your team these ten questions:
What's next?
If you answered “no” to many of these questions, now is the right time to bring structure to your process - before the next outage catches you off guard.
Let's talk:
What is currently your biggest challenge - lack of visibility, unclear ownership, or hurdles in automation?
Ready to get started? Get in touch using the keyword "CLM".
As an expert for digital identity, I look forward to discussing how we can sustainably secure and future-proof your process together.

Alexander Cornea
+43 1 60126-376
identity@bacher.at